The secret keys can/will/must be exchanged with a person or group. A back-translation is only possible with these exchanged keys! The key can be exchanged onto paper/bilet or, with even greater secret, on disk - preferably by a personal meeting.
- no mathematical cryptographic functions, the coding can be tracked by each (other)
- End-to-End encryption, regardless of the used software / Internet service
- Login into the software to read messages
- When logging in the correction of the input produces a different key = no dictionary attack possible
- When logging in, the availability is given to plug in "Password Disk" = no possible dictionary attack
- Automatic logout after five minutes of inactivity
- One-way function of the base/basic key (224 characters long), the entered password phrase can not be traced
- Repudiation is given, because each participant can get the same result
- Perfect Forward Secrecy (currently by a function "new activation")
- Deleting the master key makes all messages unreadable
- Deleting a contact folder makes the messages of the contact unreadable
- based on the first exchanged secret, a new secret can be transmitted at any time, even online

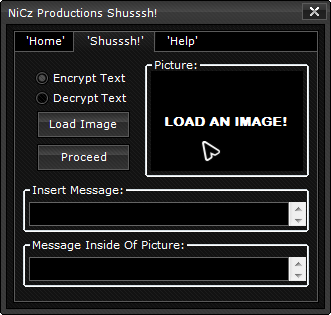
Comments not found