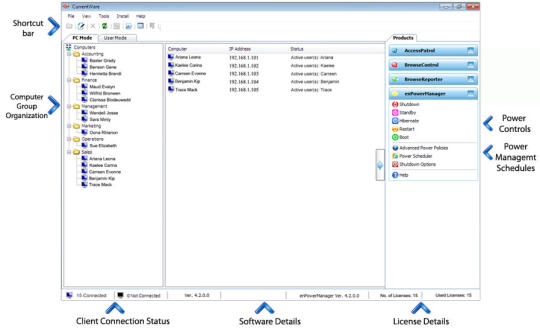
Protect your data by controlling who has access to it, how it is handled, and where it is stored. Create an allowed list of authorized endpoint devices and users, and configure modification restrictions for existing files and data. Grant temporary device access to authorized administrators by using the access code generator. Investigate endpoint activity on your network with the click of a button. Generate reports to investigate and determine where a file or program was modified and gain more insight as to how employees are handling sensitive company data and files. Generate on-demand or schedule reports to be emailed daily or weekly, and search through reports fast with the built-in table of contents and search bar.
What is new in this release:
Version 5.4.200 may include unspecified updates, enhancements, or bug fixes.



Comments not found